In its latest attack on news outlets, the Syrian Electronic Army hijacked the Twitter account of Thomson Reuters news agency.
It started with this tweet late Monday afternoon, which I re-tweeted shortly thereafter in case it disappeared (and it has).
Oh boy. RT @thomsonreuters Always via Syrian Electronic Army(@Official_SEA12) #SEA #Syria #SyrianElectronicArmy http://t.co/rjrmDzrxjU
— Mandy Nagy (@Liberty_Chick) July 29, 2013
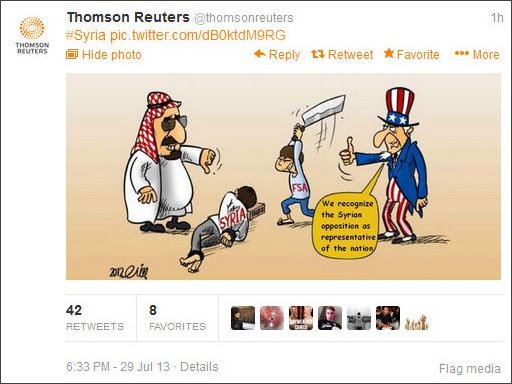
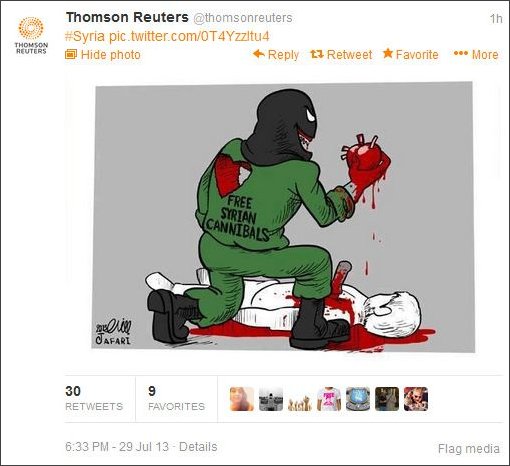
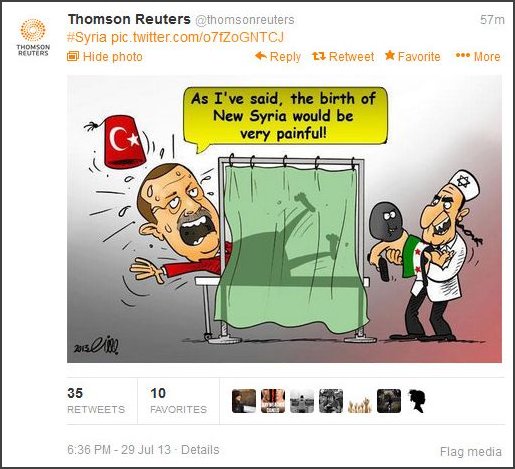
It was preceded by several other tweets containing political cartoons, which are captured here in screen shots. (Warning, they’re not exactly funny).
The Thomson Reuters Twitter account was temporarily suspended shortly after the account was hijacked, but has since been restored. This is something Twitter typically does as a protective measure when a major account has been compromised.
In an email to the Wall Street Journal, Thomson Reuters confirmed it had been hacked.
“Earlier today @thomsonreuters was hacked,” a spokesman for the news organization said in an email late Monday. “In this time, unauthorized individuals have posted fabricated tweets of which Thomson Reuters is not the source. The account has been suspended and is currently under investigation.”
As of this writing (about 7:15pm ET Monday), the Syrian Electronic Army had not yet posted a message at its own website – it often posts details there about how it infiltrated an account, website or database – so it isn’t known for sure exactly how SEA was able to gain access to the account.
But given the SEA’s usual modus operandi, it is highly possible this was accomplished through means of phishing. What typically occurs in those instances is that the hacker(s) will send an email to a member(s) of the target organization, sometimes even using a fake email address made to appear as though it’s internal or friendly to the target. The email itself will also usually be written in such a way as to appear it’s coming from an employee or colleague, and it will include a link. Clicking on the link will prompt the recipient to either enter login credentials or to login using Twitter or other social media account credentials. The hacker(s) then have possession of the credentials and can access the account without technically hacking a thing.
The phishing process can of course vary from what I’ve described, but you get the idea.
Last week, SEA hacked VOIP phone service/messaging app Viber, as well as the internet news website, The Daily Dot.
The group of hackers (or lone hacker, whichever you suspect), which is supportive of Syria’s Assad regime, has a history of hijacking the social media accounts of other news outlets, usually for the purpose of disseminating pro-Assad information or in retaliation for news coverage it deems critical of Assad. As I’ve written in numerous posts here at Legal Insurrection, SEA has previously taken over the accounts of outlets such as NPR, The Guardian, CBS, BBC, Reuters and Al-Arabiya, as well as the Financial Times, ITV News, The Onion and E!Online.
The most notorious instance of SEA’s hijacking of a news outlet is that of the Associated Press, when the hacker(s) tweeted that explosions had gone off at the White House and injured President Obama. The tweet caused the Dow Jones industrial average to temporarily plummet.
With the exception of the AP hijacking, which briefly caused some damage, SEA’s hijacking activities have been limited primarily to harmless PR stunts. But it’s important to recognize that the potential exists for SEA or any other hacking outfit to take things further and use compromised news accounts to disseminate disinformation that could have more serious consequences.
I wrote previously about an older SEA hijacking that could have been more serious had it not been quashed by an astute blogger.
In April of 2012, they hacked the Al-Arabiya news network. During that incident, the hackers disseminated messages that “the Gulf Emirates Prime Minister and Foreign Minister had been relieved of his duties and replaced by the country’s heir-apparent,” followed by a message about “an explosion at a Qatari natural gas field which killed dozens of people.” The pace at which that news spread was dangerously quick. It caused many to fear a rift within the Qatari Royal Family – had the fake news not been refuted as quickly as it was, chaos could easily have followed.
With all the global conflict in this day and age, viral disinformation has become a powerful weapon in influencing others’ actions and the public’s reaction to certain events.
Such examples aren’t meant to seem hyperbolic, that’s not my intent. Targets of such hijackings and hackings have been very fortunate thus far, as most instances have been little more than an inconvenience or even a funny episode (see: The Onion’s epic response to its own encounter with SEA). But I present the more serious possibilities only to encourage the news community to consider that the environment can change at any time.
Donations tax deductible
to the full extent allowed by law.









Comments
I think it must just be because I’m in an IT profession, but scams like phishing seem like they should never work.
And yet…
We ran a security assessment a couple years ago at my workplace where the guy running it created a fake gmail address with the name of one of the VPs; in it, he requested our internal network credentials. Nearly a dozen people fell for it (in a company of ~80).
Cyber-security, I guess, then, is one of those things that just hasn’t quite fully penetrated the general mindset yet.
Will someone hack their site and announce the death of their dear leader? tit for tat and all that 😉
At DEBKA it says Assad is close to winning. He’s closing in on Aleppo now. Once this is in his hands, Syria is back to being his. And, the rebels will have to go somewhere else to fight. Obama will be blamed because he didn’t send in troops. (Like we did in Irak. And, Afghanistan. Where the blood we shed gave America’s enemies a leg up.)
There’s still fighting going on in Libya. And, France is still in Sudan.
While Bibi went and stuck his feet into his own bear trap. Kerry, ahead, will find it entertaining to pull him around.
Yes Carol. I have not believed the rebel stuff & western media.. Syrians are not fleeing in droves .
I gotta some respect for Assad & how he has hung on.