Trump Admin Slaps Sanctions on Nine Iranians, Company for Hacking Into Universities
“Iran is engaged in an ongoing campaign of malicious cyber activity against the United States and our allies.”
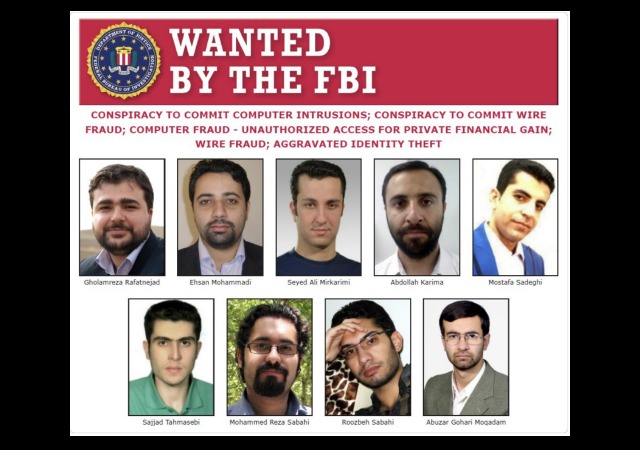
The Trump administration has slapped sanctions on an Iranian company and nine Iranians for hacking into American universities. A tenth person received sanctions after he hacked accounts belonging to HBO employees to steal data and unaired episodes of shows like Game of Thrones.
Officials said these individuals do not work for the regime, but did their work for the Iranian Revolutionary Guard Corps.
#Breaking: Nine Iranians charged with conducting massive cyber theft campaign on behalf of the Islamic Revolutionary Guard Corpshttps://t.co/DIRv5LT7E6 pic.twitter.com/EdizPpd3Rk
— FBI New York (@NewYorkFBI) March 23, 2018
The Treasury Department wrote:
“Iran is engaged in an ongoing campaign of malicious cyber activity against the United States and our allies. The IRGC outsourced cyber intrusions to The Mabna Institute, a hacker network that infiltrated hundreds of universities to steal sensitive data,” said Treasury Under Secretary Sigal Mandelker. “We will not tolerate the theft of U.S. intellectual property, or intrusions into our research institutions and universities. Treasury will continue to systematically use our sanctions authorities to shine a light on the Iranian regime’s malicious cyber practices, and hold it accountable for criminal cyber-attacks.”
As a result of today’s action, all property and interests in property of the designated persons subject to U.S. jurisdiction are blocked, and U.S. persons are generally prohibited from engaging in transactions with them.
The nine people worked at the Mabna Institute, “founded in or about 2013 to assist Iranian universities and scientific and research organizations in obtaining access to non-Iranian scientific resources.” The department stated that the company “engaged in the theft of personal identifiers and economic resources for private financial gain.”
They targeted American and foreign universities:
The Mabna Institute conducted massive, coordinated cyber intrusions into computer systems belonging to at least approximately 144 United States-based universities, in addition to at least 176 universities located in 21 foreign countries: Australia, Canada, China, Denmark, Finland, Germany, Ireland, Israel, Italy, Japan, Malaysia, the Netherlands, Norway, Poland, Singapore, South Korea, Spain, Sweden, Switzerland, Turkey, and the United Kingdom. The exfiltrated data and stolen login credentials acquired through these malicious cyber-enabled activities were used for the benefit of Iran’s Islamic Revolutionary Guard Corps (IRGC), and were also sold within Iran through at least two websites. The stolen login credentials belonging to university professors were used to directly access online university library systems.
Today, OFAC is also designating nine Iran-based individuals who were leaders, contractors, associates, hackers for hire, and affiliates of the Mabna Institute for engaging in malicious cyber-enabled activities related to the significant misappropriation of economic resources or personal identifiers for private financial gain.
The hackers stole about “31 terabytes of data and intellectual property” and the IRGC received most of that information.
They would study their subject and “then using that information to send specialized emails to the targets that appeared to come from other university professors expressing interest in a recently published work, with links to other research that were actually links to malicious websites that would mimic the professor’s login page and steal his or her login information and use it to access their accounts.”
CNN described the hacks on private-sector and government as “less sophisticated” since the hackers allegedly used “password spraying.” This means the men “collected email addresses they could find on the internet and then simply tried common passwords on those accounts, stealing email inboxes if they managed to get in.”
Others affected include employees at the Department of Labor, Federal Energy Regulatory Commission, United Nations, United Nations Children’s Fund, and the state governments of Hawaii and Indiana.
Donations tax deductible
to the full extent allowed by law.








Comments
Iran has 42 hydroelectric dams. Why don’t we start taking those dams out, one each time we connect Iran to a dirty deed?
Take a dam out and plentiful water would flow, followed by a severe shortage.
And, there would be a shortage of electricity, making it rather difficult to run centrifuges.
The FBI is looking for someone who didn’t see President Trump sleep with_______. Stop screwing around with criminals and get back to your job of undermining an election. sarc
isn’t it wonderful that we finally have a non politician POTUS who is willing to allow gov’t shutdowns…..
#MAGA
“The Mabna Institute conducted massive, coordinated cyber intrusions into computer systems belonging to at least approximately 144 United States-based universities, in addition to at least 176 universities located in 21 foreign countries:…”
2013. 2013. Gee, I wonder who was potus back then?
Hacking. Phhttt. I thought the mad mullahs would do something nefarious after former Pres. Lie All the Time released $150 billion in frozen assests and $400 million in cash airlifted to Tehran, while green lighting the mad mullah’s quest for nuclear weapons.
However, methinks many of these universities would probably have given all that cyber info, if asked. But thank allah game of thrones is safe!
Pakistan, now Iran. This has DNC collusion and influence fingerprints all over it.
So they caught a few bad apples. Big deal. I’m not impressed. These guys cannot come close to doing the damage to America that leftist professors have been getting away with for years. It’s past time to go after college staff members who openly try to destroy this country from within. Gitta rope.