NSA Contractor Charged for Leaking Classified Documents to Media
The report shows Russian hackers used phishing emails to voting officials.

NSA contractor Reality Leigh Winner faces charges for mailing classified information to a media outlet. Winner gave a report to The Intercept that shows “Russian military intelligence executed a cyberattack on at least one U.S. voting software supplier and sent spear-phishing emails to more than 100 local election officials just days before last November’s presidential election.”
The FBI arrested Winner on June 3 at her home in Georgia. She went to court on Monday afternoon.
The NSA Document
The Intercept reported:
The report indicates that Russian hacking may have penetrated further into U.S. voting systems than was previously understood. It states unequivocally in its summary statement that it was Russian military intelligence, specifically the Russian General Staff Main Intelligence Directorate, or GRU, that conducted the cyber attacks described in the document:
Russian General Staff Main Intelligence Directorate actors … executed cyber espionage operations against a named U.S. company in August 2016, evidently to obtain information on elections-related software and hardware solutions. … The actors likely used data obtained from that operation to … launch a voter registration-themed spear-phishing campaign targeting U.S. local government organizations.
This NSA summary judgment is sharply at odds with Russian President Vladimir Putin’s denial last week that Russia had interfered in foreign elections: “We never engaged in that on a state level, and have no intention of doing so.” Putin, who had previously issued blanket denials that any such Russian meddling occurred, for the first time floated the possibility that freelance Russian hackers with “patriotic leanings” may have been responsible. The NSA report, on the contrary, displays no doubt that the cyber assault was carried out by the GRU.
But the report does not indicate if the NSA concluded whether the “interference had any effect on the election’s outcome and concedes that much remains unknown about the extent of the hackers’ accomplishment.”
The Russian’s Plans
The hackers simply wanted to “pose as an e-voting vendor and trick local government employees into opening Microsoft Word documents” filled with malware that gave the hackers access to computers.
Emails were sent on August 24, 2016, to “employees of an unnamed U.S. election software company.” The NSA did not specifically name a company, but the report “contains references to a product made by VR Systems, a Florida-based vendor of electronic voting services and equipment whose products are used in eight states.” The Intercept continued:
The spear-phishing email contained a link directing the employees to a malicious, faux-Google website that would request their login credentials and then hand them over to the hackers. The NSA identified seven “potential victims” at the company. While malicious emails targeting three of the potential victims were rejected by an email server, at least one of the employee accounts was likely compromised, the agency concluded. The NSA notes in its report that it is “unknown whether the aforementioned spear-phishing deployment successfully compromised all the intended victims, and what potential data from the victim could have been exfiltrated.”
On October 27, the hackers created a Gmail address that looked like “it belonged to an employee at VR Systems.” The documents they sent out had the malware:
The NSA assessed that this phase of the spear-fishing operation was likely launched on either October 31 or November 1 and sent spear-fishing emails to 122 email addresses “associated with named local government organizations,” probably to officials “involved in the management of voter registration systems.” The emails contained Microsoft Word attachments purporting to be benign documentation for VR Systems’ EViD voter database product line, but which were in reality maliciously embedded with automated software commands that are triggered instantly and invisibly when the user opens the document. These particular weaponized files used PowerShell, a Microsoft scripting language designed for system administrators and installed by default on Windows computers, allowing vast control over a system’s settings and functions. If opened, the files “very likely” would have instructed the infected computer to begin downloading in the background a second package of malware from a remote server also controlled by the hackers, which the secret report says could have provided attackers with “persistent access” to the computer or the ability to “survey the victims for items of interest.” Essentially, the weaponized Word document quietly unlocks and opens a target’s back door, allowing virtually any cocktail of malware to be subsequently delivered automatically.
Winner
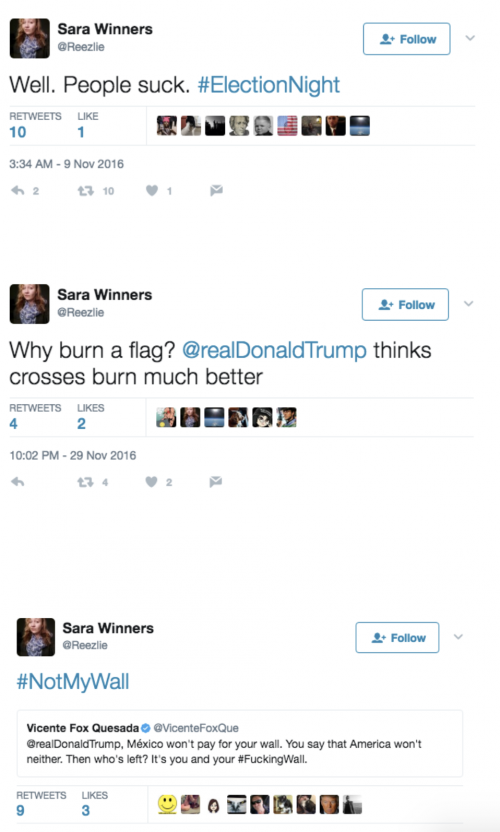
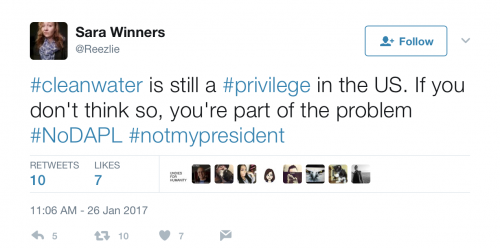
Pluribus International Corporation employed Winner and shipped her to a facility on February 13 where she “held a Top Secret security clearance.” She has been known to post anti-Trump posts on social media, like this one (from Heavy):
Heavy also reported that she set up a Twitter account under the name Sara Winners, which she used “to comment on a slew of political things, such as the North Dakota Pipeline and politics.” She also served “as an active member of the U.S. Air Force.” From Mashable:
The Department of Justice noted that Winner spoke to agents as they served out the search warrant:
During that conversation, Winner admitted intentionally identifying and printing the classified intelligence reporting at issue despite not having a “need to know,” and with knowledge that the intelligence reporting was classified. Winner further admitted removing the classified intelligence reporting from her office space, retaining it, and mailing it from Augusta, Georgia, to the news outlet, which she knew was not authorized to receive or possess the documents.
The NSA found out she printed off the report through its auditing system. Six people printed it off. Only Winner “had been in email contact with the news outlet.” And it looks like The Intercept ratted her out:
.@theintercept blew its source's cover by giving the NSA a copy of the leaked document, according to @nytimes https://t.co/PG73Pqe4ZX
— Josh Rogin (@joshrogin) June 6, 2017
 DONATE
DONATE
Donations tax deductible
to the full extent allowed by law.










Comments
What a moron. She will probably end up in prison unless she gets a radical left wing judge. It’s scary to think of people like her having access to top secret stuff.
MORE FAKE NEWS – from the Reality Weiner.
Maybe it’s a fake document as well. She alone or in concert with somebody else could have created that document, it seems to me.
She goes to work with a high security clearance after Trump takes office, and two or so months later she produces an alleged NSA document for a publication set up to clandestinely receive such material, then she readily confesses to the entire caper. Am I the only one who sees something suspicious about the alleged document?
From what I understand, the net effect of the document is that it delegitimizes the election results. If Hillary had won, would Winner still have done the same thing? I think not.
Certainly. And “leaking” it to the Press would give it a gravitas it may not merit.
They’re desperate for a shred of evidence that the entire Russiagate fantasy is real. This report isn’t itself evidence, but from their viewpoint, it’s better than nothing.
Going through life with a name like Reality Winner probably drove her insane.
I’m pretty sure that progressivism drove her insane and THEN she changed her name to Reality Winner.
Seriously, what on earth are they doing giving security clearance to anyone who is such a blatant, partisan, SJW hack?
Whoever gave her the clearance should be fired.
The Air Force gave her the clearance which they’re good for 5 years. Her birth name is indeed Reality Winner and is in the Vital Records for the State of Texas. The Mormon Church also has this record archived and Ancestry.org has the print out of her name from Texas vital records as well.
https://familysearch.org/ark:/61903/1:1:V8YB-HP6
I read somewhere online earlier today that she had legally changed her name. I don’t know if that’s true or if doing so results in updates to the types of records that feed sites like what you linked.
Regarding the security clearance, I guess that’s not too much of a surprise, is it? After eight years of that traitorous, limp-wristed Marxist pansy Obama shitting in the well of the US military it is now infested with a bunch of cross-dressing, SJW morons.
God help the USA if we ever go to war against a serious adversary again. “Fundamentally transformed” indeed.
…..and now for the arrest and prosecution of sHillary Clinton and her sleazy minions….
She is gonna get loved so hard in prison!!! 🙂
and on a serious note…who the hell carried out her background checks and thought it a good idea to get her a top secret clearance???
Apparently she had recently served in the military and had her security clearance because of that.
So basically no one carried out any background checks on this chick then. Seems to me that someone needs to review this companies clearances eh?
You’d be surprised at the number of morons in the military who have TS clearances. The penalties are usually more severe though when you do dumb stuff with a TS clearance in the DoD. If you’re in the DoD – go directly to jail. If in State or another department you get your name on the election ballot.
having a clearance in the military only means she had a good chance of getting one in a civilian job, the the investigation is completely redone.
So the news agency (word is it’s Anderson Cooper) knowingly received top secret documents and then used them for a story. What are the charges for them? I also believe that Pluribus International Corporation should have all of their clearances pulled as they either have trouble hiring trustworthy employyes or purposely cleared her to be a mole.
None, as long as they notified the government, which is what they did. Pentagon Papers case. (Ellsworth)
I hear she’s now getting her name legally changed to Reality Check.
I think we have a winner for comment of the day.
Yes, probably the entire week.
Truly sad state of affairs when we have raise people that are so totally out of touch with rational behavior.
This snowflake probably thinks she should get a trophy for believing she can and should do WHATEVER SHE THINKS is OK.
It certainly does look like she let her hatred for Trump trump her love of her Country.
I followed a link to her Facebook page last night.
She was taking quite a lot of chit from a lot of people, but she had no shortage of defenders on there calling her a “hero” who “should get a medal”.
It’s amazing someone with a top secret clearance would leave such a clear trail of tracks to identify her.
I don’t think the “intelligence community” has any secrets because they don’t have adequate controls. Snowden walked off with millions of documents. They gave clearance to a low level gender confused druggie Army private who walked off with a huge trove. And those are the cases we know about. How many people have stolen crap that has either gone undetected or authorities are too embarrassed to admit it publicly (and that info has been sold to Iran, Russia, etc.)
We’re paying 17 intelligence agencies $50 billion a year and what are we getting for it? It’s looking like a jobs program. I’d rather pay them to dig holes and fill them back up rather than pay them to steal classified info.
She got outed because The Intercept showed the FBI the *actual* document that was leaked to them, and didn’t just describe it.
I didn’t realize that up to date printers put so much encoded information on pages that they print. Of course, I’ve never allowed myself to be put in a situation where I would have to worry about that.
Here’s a technical explanation of how they identified her so quickly; quite fascinating.
http://blog.erratasec.com/2017/06/how-intercept-outed-reality-winner.html#.WTayHWjyuUl
“I don’t think the “intelligence community” has any secrets because they don’t have adequate controls.”
Humans have been, are, and always will be the weak link in any security system (3 can keep a secret only if 2 are dead). No matter how robust the safeguards, and individual with the will and the access can (and eventually will) violate security protocols.
“Spear-phishing emails”?
Fauxcahontas will not like that phrasing.
We were told that three WH leakers were identified when President Trump was on his international trip. Who are they?
https://twitter.com/Reezlie/status/828956117338292224
used to be mp in germany dealing with nuke security (so had to deal with multiple prp evals) as well as feeding mpi possible security leak info.
she is the epitome of stupidity.
tweet didn’t embed, heres the text
There are many Americans protesting US govt aggression towards Iran. If our Tangerine in Chief declares war, we stand with you!
I also got screenshot
The lefty media will try to portray her as a crusading whistleblower who found “proof” that the Russians hacked stuff.
Throw her in jail.
For someone who clearly hates our country, why was she in the military?
Which media outlets received the information? I haven’t seen that anywhere.
The Intercept.
https://theintercept.com
She gained her clearance in 2013. She wasn’t in the Air Force for terribly long. I suspect she loved her country and her military so long as a Democrat was in the White House.
I’d have to go flipping through her social media, but I suspect she was radicalized by Buzzfeed, Slate and the MSN. This is the natural consequence if you only become proud of your country after an election.
She frightens me…. as in, she frightens me to see what our young people think.
Rush Limbaugh talked about it a few months ago, that they see the future as a dark place, and she does, if you read her twitter feed. She said she wouldn’t want to have kids because she’s afraid of “climate change” just for her CATS. Her cats, with a max lifespan of 20 years….
If our young people think this way – and evidently they do — it’s no wonder we’re being replaced by foreigners who have oodles of children at our expense.
She’s very left on very many things. Her twitter feed shows what you’d expect from someone very very left.
What do you expect from a product of the left wing indoctrination centers known as our public schools.
Ever notice the comments section in major newspapers when there is an act of animal cruelty vs. assault on a child? The animal related stories will get 10-20 times the number of comments compared to the human related story.
This generation has humanized pets and de-humanized human beings (via abortion on demand). Many of them are truly frightening in their “logic”.
What people are missing, I believe, is that Ms. Winner is the “Deep State”. These folks are centralized. They have no membership cards or meetings. They’re, instead, idealistic partisans who act in a manner that they believe the collective body of partisans, like them, would agree. It’s a “wink and a nod” and all done because they’re smarter, better and gosh darn it more compassionate. Remember when the voting public disagrees with them the response is, “people are stupid”. It’s like the IRS issue. Sure the IG admitted the IRS used “inappropriate critera” and acted “inappropriately”. But there was no specific order as there was no need for it, everyone understood and knew what was expected in a partisan world. It’s a “wink and nod”. Even the POTUS when asked, knowing what the IG has found tells us, with a smile, “there’s not a smidgen of corruption”!
This, imo, is exactly what’s wrong with our government at every level and I’ve no clue how to purge it.
Dear WillS68:
It’s pretty clear the way to purge it is extraordinarily hard:
END CIVIL SERVICE.
Go back to patronage.
But you’ll have them screaming and yelling the usual horrible things.
From what I read, she isn’t civil service. She works for a contractor. Maybe we should quit using contracted services?
Eh. That’s treating a symptom, not the disease. The disease is a fundamental contempt for the idea that the law applies to everyone equally. The idea that a Republican/Trump voter/pro-lifer/whatever out-group has the right to be treated exactly as the in-group is foreign to her.
It’s a fundamental failing in education and instilling principles in Millennials. I’m not sure it can be fixed, absent a five-part series on the Daily Show.
That’s not really the problem here. I believe someone already noted this but she got her clearance through the Air Force and it was still valid.
You can go to any military contractor web site and you’ll see all sorts of jobs advertised where the successful applicant must either have or be eligible for a security clearance. But getting a security clearance is a lengthy, expensive process and always something of a gamble. The job candidate may not even know if they have something in their background or sufficient foreign contacts of a particular type to disualify them. If an applicant walks in who already has a clearance that’s a sure thing. In fact a contractor will often prefer to hire a candidate with a clearance but no relevant background and teach that candidate the job skills then to hire someone who has the perfect skillsets for the job and then gamble that they can go through the often two year process and actually get the clearance.
The contractor may have understandably believed that since the Air Force gave her that clearance she was trustworthy.
So, how the hell did she get a clearance from the military? The fact that DoD is giving people like this clearances is the real problem. Isn’t one Chelsea Manning enough?
Dear WillS68:
Also, one more thing:
It’s “Miss Winner,” as in, she’s single. It took me a long time to understand why “Miss” and “Mrs.” are so important. Here’s the reason: it’s a man’s role to chase. That’s how courting works on the real world. So, if a woman is a “Miss” then the man knows she’s available and he is able to pursue her.
We have too many kids born in the wrong circumstances and a contributing reason is that we’ve destroyed our courting mechanisms and not replaced them with anything remotely functional.
thanks.
*fat fingers, small phone: should’ve been, “are NOT centralized”.
She’ll assert the Hillary Clinton Defense: “I had no criminal intent.”
Yes, and that works really well when your name is Hillary Clinton but not when it’s Reality Winner. Or, anything other than Clinton for that matter.
Everybody still okay with the NSA spying on American citizens without warrants? Thank God for Edward Snowden.
I hate to generalize but I will anyway. I have a daughter who is a millennial and she is a wonderful person but she has the millennial attitude of “Live and let live”. She is nonjudgmental and thinks that all people are basically good. Although she hates violence she can see in some instances the “Other” viewpoint. When I bring up the inherent violence of islam she rejects that islam is violent and only the few are radicalized. She is a beneficiary of capitalism but doesn’t see anything wrong with Socialism. She thinks all people should have free healthcare but all should pay into it like Medicare. She is very bright and can hold her own with me in a debate about these subjects. I say all of this because millennials are like this more than any other group in American history. We are looking at a group for the first time that does not feel a kinship to the past. This leaker, while certainly not like my daughter, is a person who has been fed America hate her whole education and is now the “Freedom Fighter” that she was told she could be against the “Great Satan”, America. The anti-Trump crowd is full of these people and they are going to be a force to be reckoned with. It is bewildering to see this happening in our great country but with the slant of our schools today, away from nationalism, this is the consequence. Our hatred of spies and traitors is not shared by this group. God help us.
“Live and let live” unless you are pro-life, opposed to gay marriage, believe that there are only 2 genders (with extraordinarily rare exceptions) or question the science behind human-caused global warming.
Was thinking that Ms. Winner was probably acting out of a whistleblower mentality and that we would soon be learning how the report on Russian hacking had been buried instead of being sent up the chain and laterally for review.
However if her apparent tweet to the Iranian foreign minister is accurate, and she really did say that in the case of war she stands with Iran (!), then I am not sure I have any more time for her.
“She replied to the Foreign Minister of Iran saying she’d “stand with” Iran over America if Trump declared war:
Sara Winners @Reezlie
“@JZarif There are many Americans protesting US govt aggression towards Iran. If our Tangerine in Chief declares war, we stand with you!”
Troubling.
Another day, another baby hunt. The information is real. The analysis was done through inference. The same logical arguments that have corrupted science, are also a clear and progressive problem for the integrity of government and press.
Ms. Winner did it all wrong. She should have set up a private email server and used it to store all her top secret documents, making sure word gets around that 100 percent of her government work involving classified documents is on a unsecured system.
Then, when confronted by the FBI, erase the server, say it was not intentional and totally legal.
During the cold war, a security check involved investigating membership in the Communist Party, association or activism in radical movements, and the like.
Sadly, it looks like association with the Democratic party and liberal movements is now necessary.
Final word, Ms. Winner needs to serve as an example. Not less than 10 years in the pen., hard labor, and maximum fines will do.
Or 30 days in the electric chair after a military court finds her guilty of treason and espionage (like those WWII German spies caught soon after landing by u-boat on the NJ shore).
I was hoping she would be the head of a long line.
Reality Winner, meet Hillary Loser.
Has everyone forgotten that it was Homeland Security that was attempting to hack into some State voting sites before the election?
But that would most likely benefit Democrats… so its ok.
I see nothing at all in that story which implicates Russian officialdom. The big explanation is about the hack tactic; the only major actor to blame there is Microsoft, which built in the vulnerability which could be exploited (and not for the first time, either).
But that stuff is routine, and has nothing at all to do with Russia.
It looks like a common rhetorical trick which I often see in leftoid screeds. Make several statements, and the wilder the accusations, the better. Then explicate the least offensive of those at great length and excruciating detail. That makes it look like you’re really on top of the matter, even though you’re just describing a scenario which, however plausible, is hardly established fact. But the mass of detail will con casual readers into thinking that you’ve nailed the problem solidly; even if they don’t really understand it, it will work because people are often unduly impressed by things they don’t understand. Then stop there—the most important part of the deception is to leave those same casual readers with the impression that you’ve not only demonstrated the obvious veracity of that one claim, but also the more outrageous claims which you didn’t discuss at all.
In this case, yes indeed, an intrusion as described is technically possible. And the intrusion may indeed have happened in the way described, although no evidence for that seems to be cited. But implication of Russian agencies is not explicated at all. And we’re all supposed to be impressed with that.
So … to me it looks like this moron’s cookies are in the vise, and all for leaking what is more than likely a garbage report.
Reality Winner was childish. The lack of considering consequences seems very tweenish. When society pushes “childhood” into the mid-20’s, this is what can be expected.
Good point. She very well may still be on mommy’s insurance.
Which is exactly why we should go back to the tried and true paper ballot and stylus punch. Electronic machines and computers are asking for viruses and hacking.
didn’t work that well in Detroit, the vote counter just kept reading them in time and time again