ISIS Sympathizers Hack CENTCOM, Post Sensitive Information
“AMERICAN SOLDIERS, WE ARE COMING WATCH YOUR BACK”
Hackers claiming a connection with the Islamic State have taken control of two social media accounts owned by the U.S. Central Command.
Via the Washington Free Beacon:
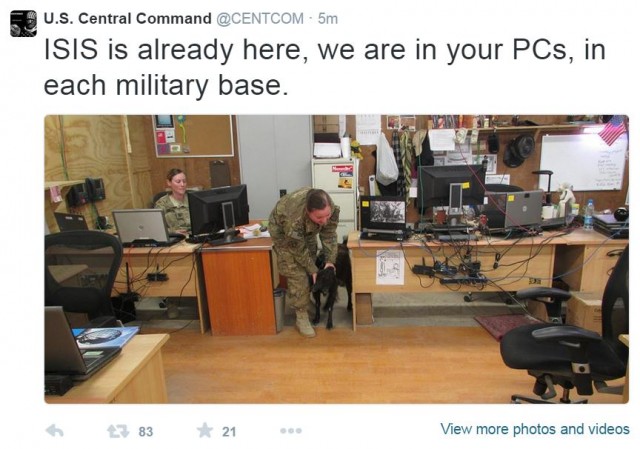
“ISIS is already here, we are in your PCs, in each military base. With Allah’s permission we are in CENTCOM now,” said one tweet sent from CENTCOM’s account.
The apparent hack came as President Obama addressed the nation regarding cyber security. He is expected to propose two pieces of cyber security legislation and to address the effort in his upcoming State of the Union address.
The hackers subsequently tweeted images of spreadsheets containing the home addresses, phone numbers, and email addresses of dozens of current and former senior U.S. military officers.
“AMERICAN SOLDIERS, WE ARE COMING WATCH YOUR BACK,” one tweet stated.
The hackers have also posted to PasteBin sensitive and personal information they claim they obtained by breaking in to mobile devices.
A search of the Google cache reveals the tweets posted to CENTCOM’s now-suspended Twitter account:
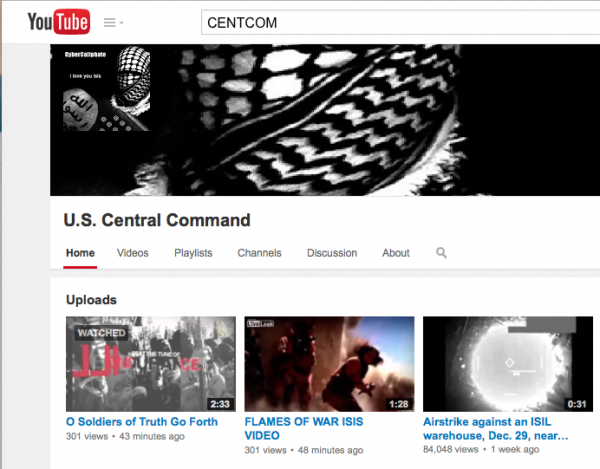
I grabbed a few screenshots of CENTCOM’s YouTube account, which also appears to have been compromised in the cyberattack:
Twitter, of course, is on form in its response:
Why the CENTCOM Hack is Actually a Good Thing
— Cameron Gray (@Cameron_Gray) January 12, 2015
The @Centcom hackers have been sent to Twitmo making Twitter officially tougher on terrorists than Obama. #Gitmo
— Ben Howe (@BenHowe) January 12, 2015
We’ll keep you updated if and when the situation develops.
 DONATE
DONATE
Donations tax deductible
to the full extent allowed by law.












Comments
Everything posted is available in the public domain. Hacking CENTCOM’s twitter account is far different than hacking CENTCOM itself. Teens hack each other’s facebook and twitter accounts every day. The maps offered, for some reason, are of North Korean and Chinese nuclear sites. Why? I asked the retired USAF guy next office over if it’s hard to get lists of US military officers. He didn’t know for sure, but didn’t think so.
The hacker is clearly in support of ISIS -or- is against Obama and just using ISIS to gig him, since the twitter hack came while Obama was publicly speaking of his proposed cyber security initiatives.
Personally, I think George Bush is down in his mother’s basement sitting at a keyboard and laughing his ass off as he high-fives a teenaged nephew.
Given the Obama administration’s demonstrated computer nous (hi, healthcare.gov!), what bet the official Youtube and Twitter passwords were set to “PASSWORD”?
Uh oh, they’re in our computers.
Now we’ll need a squad of tiny commandos to get them out.
I had a palmetto bug in my Apple™ once.
They clearly intend to do here what they did in Britain. I expect it will be public.
We can choose to take that threat seriously or pretend that it just won’t happen here. The Obama administration is clearly taking the latter approach.
On the bright side, every vet I know answers the door with a loaded gun in his non visible hand. On the less bright side, I expect these cowards will choose an elementary school surrounding a base stateside or something of that nature and do what they did in Pakistan. We’ve already seen how soft of targets our schools are and our reluctance to make them targets that bite back.
They’ve hacked a Twitter account. And a public Youtube channel. And as Henry points out above, that’s nothing more than what teenagers do to each other on a daily basis.
There’s a fair chance ISIS had nothing to do with it either.
Settle down, especially with that gun in your hand. You’re liable to shoot your local Avon Lady like that.
Besides, if anything happens, it won’t be islamic terrorism. Just some good old fashion workplace violence.
I have three simple questions (that will never, of course get answered):
#1) Who was responsible for protecting the hacked systems from the hackers?
#2) How much was that person or company paid?
#3) When will that person/company be fired?
#1) Who was responsible for protecting the hacked systems from the hackers?
Twitter and YouTube’s IT security personnel. CENTCOM wasn’t hacked, their Twitter and YouTube accounts were. No biggie, a daily event.
#2) How much was that person or company paid?
Market wage for a website security techie?
#3) When will that person/company be fired?
Never. Twitter and YouTube don’t promise hack-proof accounts. However, if the haqck occurred because somebody was asleep at the wheel, that the hack wouldn’t have succeeded without a specific dereliction by a staff member, I suppose they’d be disciplined, possibly fired.
“I expect these cowards will choose an elementary school surrounding a base stateside”
Let me just say, that if they pull a Breslin here the backlash should make the what the Romans did to Carthage mild.
Hack into the computers that have Obama’s college transcripts, his LSAT score and his grades at Harvard and I will be impressed.