FBI Investigating Scheme to Impersonate Trump’s Chief of Staff
WSJ reported that the responsible party used Wiles’s personal phone, not her government phone.
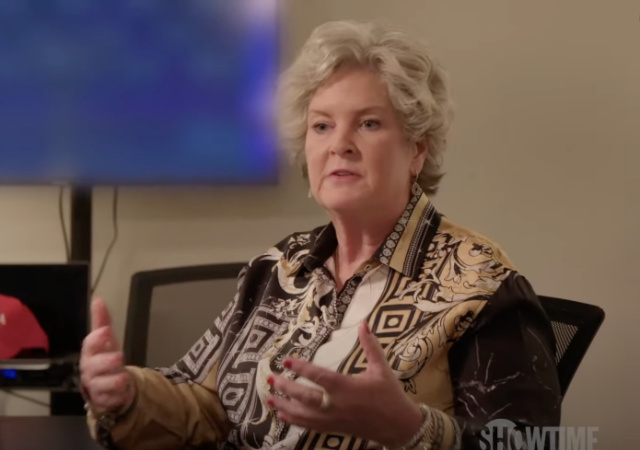
Federal authorities have started investigating a scheme to impersonate Susie Wiles, President Donald Trump’s chief of staff.
From The Wall Street Journal:
In recent weeks, senators, governors, top U.S. business executives and other well-known figures have received text messages and phone calls from a person who claimed to be the chief of staff, the people familiar with the messages said.
But the messages weren’t from Wiles—and the Federal Bureau of Investigation and the White House are trying to figure out who is behind the effort and what the goal is, according to some of the people. FBI officials have told the White House they don’t believe a foreign nation is involved, some of the people said.
“The White House takes the cybersecurity of all staff very seriously, and this matter continues to be investigated,” a White House spokeswoman said.
“The FBI takes all threats against the president, his staff, and our cybersecurity with the utmost seriousness,” FBI Director Kash Patel said in a statement. “Safeguarding our administration officials’ ability to securely communicate to accomplish the president’s mission is a top priority.”
WSJ reported that the responsible party used Wiles’s personal phone, not her government phone.
At first, the recipients found the messages authentic, especially since the voice sounded like Wiles.
Investigators believe “the impersonator used artificial intelligence to imitate Wiles’s voice.”
One message asked someone to list people Trump could potentially pardon.
However, the people became suspicious when the person made obvious mistakes:
It became clear to some of the lawmakers that the requests were suspicious when the impersonator began asking questions about Trump that Wiles should have known the answers to—and in one case, when the impersonator asked for a cash transfer, some of the people said. In many cases, the impersonator’s grammar was broken and the messages were more formal than the way Wiles typically communicates, people who have received the messages said. The calls and text messages also didn’t come from Wiles’s phone number.
Suspicions continued to escalate when the impersonator sent messages while Wiles was traveling to the Middle East with Trump.
Unfortunately, those who believe the person was Wiles interacted with them before Wiles notified everyone of the breach.
Donations tax deductible
to the full extent allowed by law.








Comments
Perhaps this is an example of phone number spoofing. If so, arrest the telecommunications industry executives who decline to stop making it possible. And the politicians who refuse to stop them.
I am not up on these things, so, please explain HOW the spoofing can be stopped. Does the technology actually exist or is it something folks demanding it want to believe exists? I just plain don’t know. Thank you.
Like anything else – by severe punishment of anybody that engages in it.
The ‘benefits’ of spoofing numbers are very low, but right now the risk is nonexistent because there are no real penalties for it.
Start levying million dollar fines for every instance of a company spoofing a number and watch how fast it disappears.
Gibbie wants to go after telecom execs for not stopping it. I don’t see how with my knowledge of how a phone works stopping at Strowger technology.
I fully agree: find the spoofers themselves and go after them full steam.
There does come a point at which the telecom execs DO become complicit.
There was a time where they were forced to label nonsense calls like this ‘spam likely’. So they obviously are capable of detecting it when they actually want to put the slightest effort into it.
At it’s core, there is a laughably easy fix that they are REFUSING to implement, despite growing demand. Namely – allow users to set their phone to ignore ALL calls from numbers not in your contact list. Anybody not in your contact list doesn’t even show up as a call, they are sent straight to voicemail, and they are REQUIRED to enter a callback number in order to leave a voicemail.
That would eliminate 99% of the scam and spam calls.
But of course they refuse to do that.
Um…. my iPhone does in fact offer that option.
But as a self-employed individual, I don’t want to reject calls from new clients.
Frankly, my personal spam problem is text messages over phone calls, by a landslide. And damn near every one of them are Republicans looking for donations. You can text STOP, but you’re texting it to a one-off phony number they don’t intend to use again anyway. And even then, I have actually gotten solicitations from a DIFFERENT Republican from the same original number I already STOPped, so STOP is a placebo to boot.
As an erstwhile young phone phreaker, I can assure you that when a telecommunications company WANTS to prevent fraud, it finds the technology to do so. When the stakes were free long distance and international calls (loss of revenue), the Bell System had its exchanges locked up to the teeth within six months. The fact that phone spoofing fraud has been allowed to exist for over a decade tells anyone with two brain cells to rub together that it will prove upon investigation to be an actual source of revenue for the carriers.
Any speculation as to how the carriers are benefiting from the spoofing?
My point EXACTLY!
Wait, the FBI is investigating crimes now, and not political opponents? Will wonders never cease.
Now, now, NOW! They do more than investigate and set up political opponents. They actively observe lone wolves affiliated with known actual terrorist groups so that when that lone wolf affiliated with a known actual terrorist group does something, they can say the person was under observation, is a lone wolf, and no motive is apparent.
Only to the extent that high-level politicians will get their phones secured and their stolen purses back. You won’t.
The democrats will stoop to anything.
Nigerian princes
“ and in one case, when the impersonator asked for a cash transfer”
LOL! They could have used the old I’m in jail and need to be bailed out.
“I need bail for President Trump, who is in jail for 47 felonies.”
–Script found during FBI search of tjv1156’s playhouse
Look to Comey and his buddies. They’re treasonous, and think they’re very clever.
While you’re at it stop the damn India based telesales calls claiming to originate from my town, Either that or isolate India for not shutting down the telesales firms.
The telecoms sell them the ability to do that.